Most phishing attacks don’t start with something super obvious. They look like normal emails. It could be a vendor request, a guest inquiry, a message from your boss. Phishing emails are usually something your team is used to seeing and responding to every day.
This is exactly what makes them so dangerous.
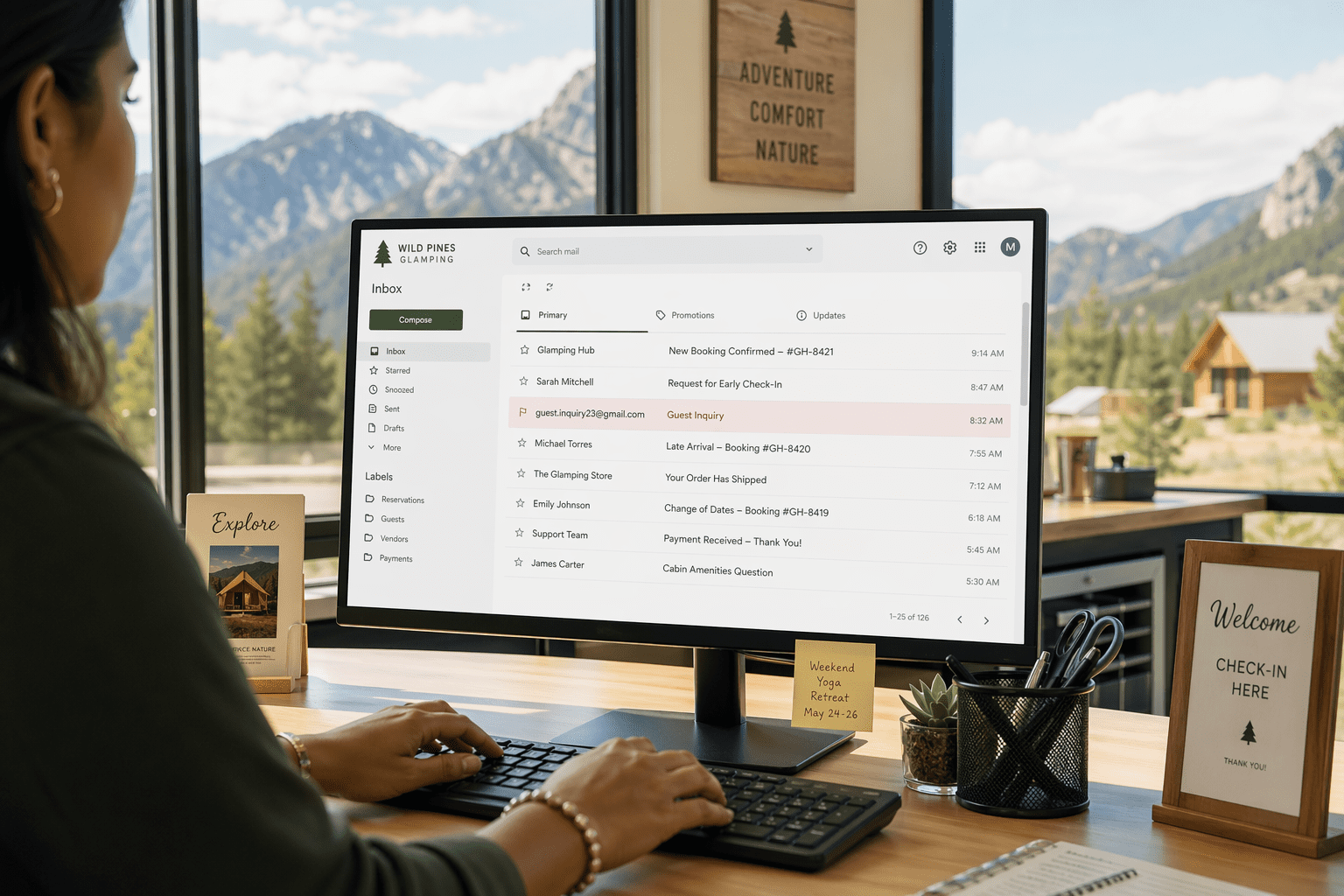
We recently responded to an incident where a phishing email came through posing as a Booking.com guest. Nothing about it raised a red flag. In a busy environment, especially one where emails like this are expected.
From there, the attack chain started. The difference between our client and a lot of business who fall victim to an attack like this regularly is that this attack didn’t get very far.
Here’s how we stopped a potential business disaster in its tracks and saved our client time, money, and their reputation.
What Is a Phishing Attack?
In simple terms, a phishing attack is when a bad actor tries to trick you into clicking, downloading, or sharing something they shouldn’t. Usually, by pretending to be someone you trust.
It typically comes in an email that looks legitimate. Something routine enough that you don’t think twice about it. Behind that email is a hidden malicious goal: to get you to click a link, download a file, or enter your login information.
From there, the attacker tries to gain access to your systems, your email, and your data.
The tricky part is that it rarely looks suspicious. Especially these days, when cyber criminals have learned that their success comes from being as convincing as possible.
This is why phishing is still one of the most common ways attacks start. Your people might be super careful and have great email hygiene, but if an email looks like something you’d normally trust, you’d likely click it too.
About Our Client
Our client is a well-established, high-volume RV resort that operates year-round and serves hundreds of guests at a time. With over 500 campsites and a steady flow of reservations, inquiries, and guest communication, email plays a hyper-critical role in their day-to-day operations.
Like many teams in hospitality and reservations-based environments, their staff is constantly reviewing and responding to incoming messages. It all moves quickly, and there’s not much room for delay.
They’ve built their reputation on delivering amazing guest experiences, which means that their team is trained to be responsive, helpful, and efficient.
This is exactly what makes them an ideal phishing target.
A Trusted Email, A Malicious Sender
The phishing attack started the way most of these do: with a normal-looking email.
It came through as a guest inquiry, something their team sees and responds to every day. Nothing about it immediately stood out as suspicious, especially in their reservations environment where emails are constantly coming in.
At some point, the email was opened and interacted with.
Behind the scenes, that triggered a malicious download (a zipped file that looked harmless) containing a hidden script designed to execute in the background. From there, the goal was to pull additional payloads and establish deeper access to our client’s system.
This is where things can escalate quickly.
A single interaction can turn into a nasty chain reaction of compromised credentials, unauthorized access, and movement across the network.
But in this case, that chain was interrupted almost immediately.
Stopping The Chain Reaction
As soon as the activity was detected, we moved quickly to contain the situation and understand exactly what happened.
Step 1: The affected device was immediately isolated from the network using Crowdstrike. This stopped any potential spread and prevented the system from communicating externally while we investigated.
Step 2: Then, we worked through the affected account itself. All active sessions were terminated in Microsoft Entra ID as a precaution, making sure that if anything had been accessed or tokens were captured, they were no longer valid.
Step 3: We tracked down the source of the issue: the phishing email. It was removed from the inbox to prevent more interaction, and the sender was blocked to stop any new messages from coming through.
Behind the scenes, we analyzed the file that was downloaded to understand what it was trying to do. The script attempted to run in the background and pull in additional payloads, but it was blocked before it could execute.
That’s where layered security came into play.
The Technical Side
CrowdStrike detected the suspicious behavior and killed the process almost immediately. At the same time, ThreatLocker blocked the unauthorized scripts from executing, preventing the attack chain from continuing.
Together, those layers stopped the attack before it could:
- Download additional malware
- Communicate externally
- Move across the network
We then validated the rest of the environment to confirm there was no spread, no additional activity, and no lateral movement.
Once everything was confirmed contained, the final step was wiping the affected system to fully eliminate any remaining risk and return it to a clean state.
The Results
Because the right protections were in place, this incident never escalated.
The attack was detected early, stopped mid-execution, and contained before it could spread beyond a single device.
No second-stage malware was downloaded, no lateral movement across systems occurred, and no data was accessed or exfiltrated.
What could have turned into a full compromise was reduced to a contained event with minimal impact.
Just as importantly, we were able to see exactly what happened from initial email to attempted execution by using telemetry from CrowdStrike and Threatlocker. That level of visibility made it possible to validate that nothing was missed and the environment was fully secure.
The system was wiped as a final precaution, and our client was able to continue operations without disruption.
What could have been a disaster had they not had the right tools in place turned into a simple learning experience that their team will carry with them.
About Network Thinking Solutions
Network Thinking Solutions is a managed IT and cybersecurity provider that helps businesses protect their systems, support their teams, and scale with confidence.
We specialize in working with organizations that rely on uptime, communication, and fast-moving operations where even a small disruption can have a big impact.
Our approach is built around layered security and real-world response. That means not just putting tools in place, but making sure they’re configured correctly, monitored consistently, and ready to act when something happens.
From endpoint detection and response to zero trust controls, email security, and cloud management, we focus on building environments that are secure, resilient, and easy for teams to operate within.
Because at the end of the day, it’s not just about stopping threats, it’s about making sure your business keeps running smoothly when they show up.
Are you ready to add that extra layer of protection? Contact us for a complimentary consultation.