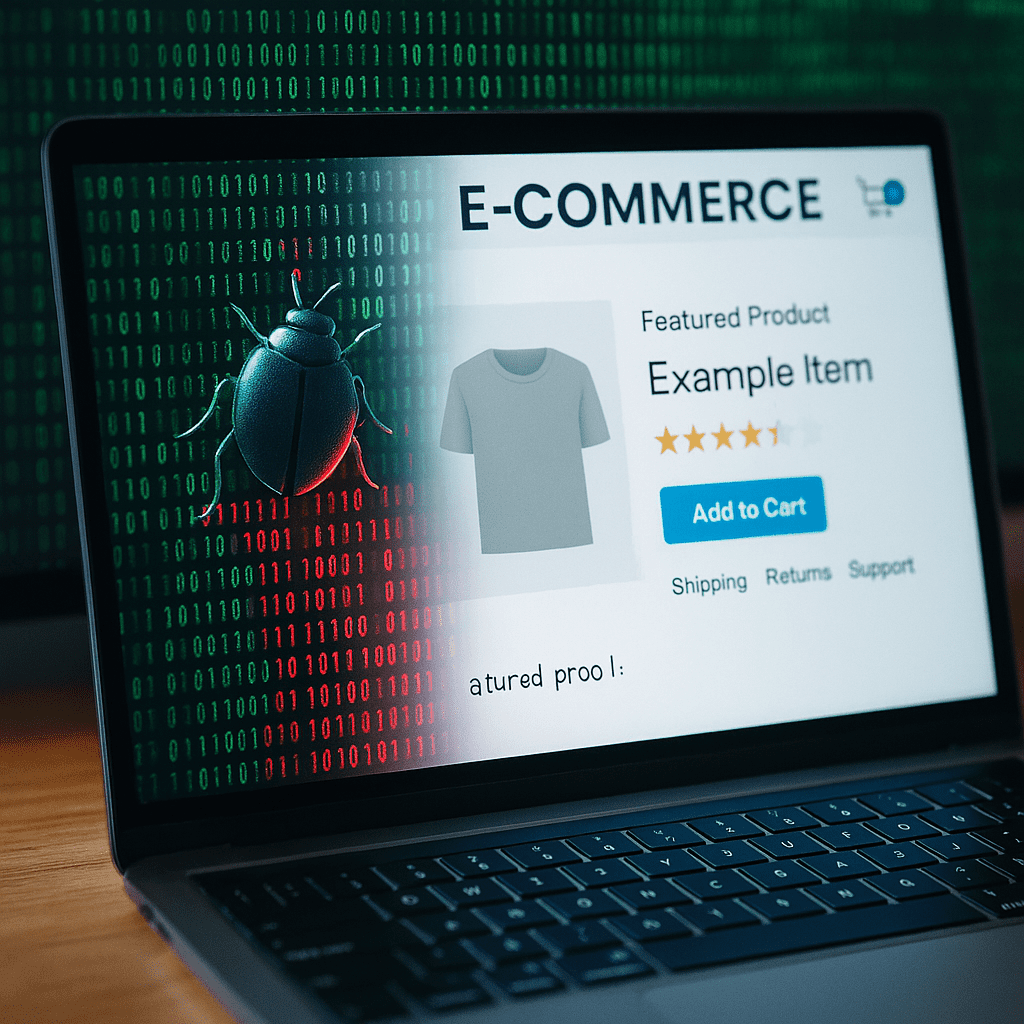
Malicious code hides in website funnels like CheckoutChamp. Learn how attacks slip in, the risks they pose, and steps to stop them.
Tag Archives: cybersecurity
What Is an IP Checker and Why Should Businesses Use One?
Learn what an IP checker is, how it works, and why it matters for business security, remote work, and spotting risks before they escalate.
Employee Offboarding Procedures: Why an IT Checklist Is Essential
Learn the hidden risks of poor offboarding and how an IT process can protect your company from data loss and compliance headaches.
Cloud Security Isn’t Automatic: What Your Business Might Be Missing
Cloud security isn’t automatic. Learn the gaps most businesses miss, and how NTS helps keep your cloud secure and under control.
When Internal Isn’t Safe: The Quiet Threat of Direct Send Phishing
Microsoft 365’s Direct Send feature is being exploited for internal-looking phishing. Learn the risks and how to protect your business.