Real estate deals move fast but so do cybercriminals. Here are the hidden risks inside every CRE transaction and the steps that keep you safe.
Tag Archives: cybersecurity
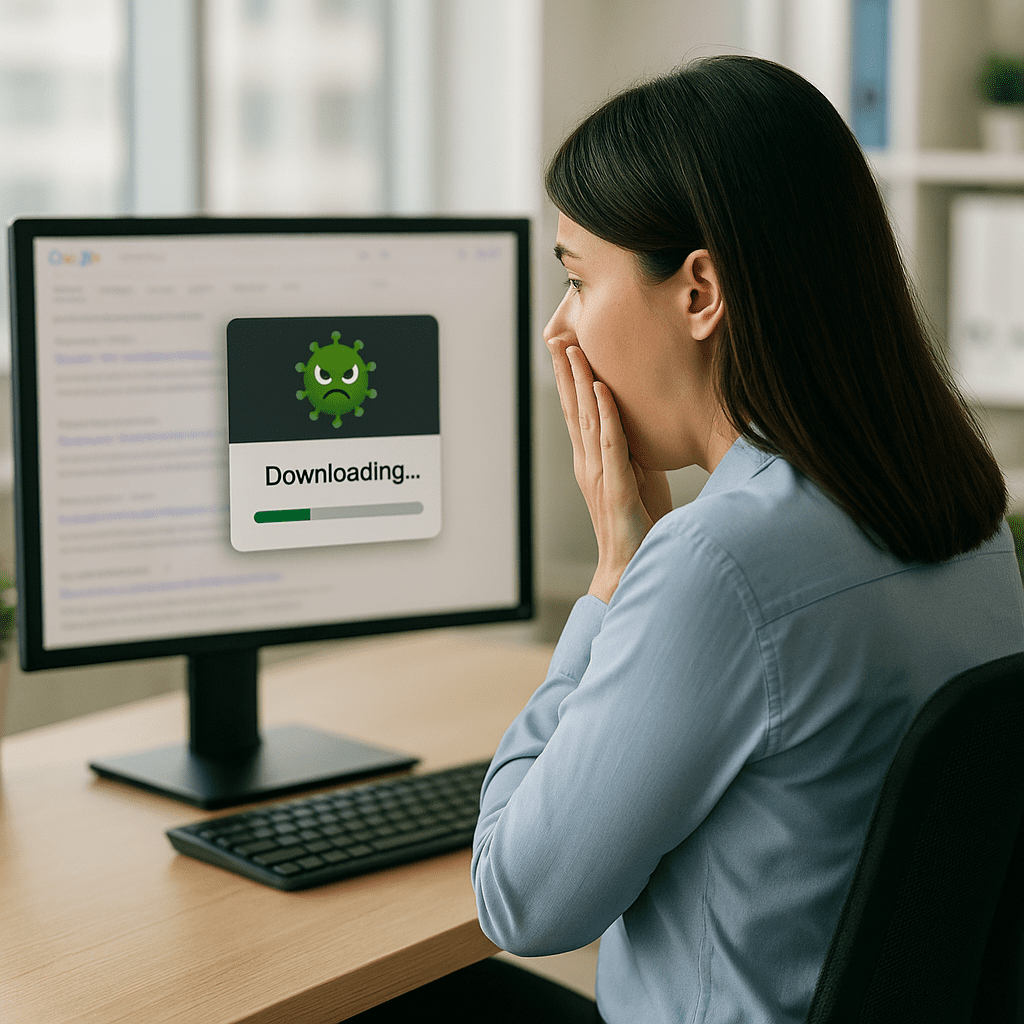
Zero Trust Matters: How Malicious Google Results Are Driving the Next Wave of Breaches
The case is gone, but the warning isn’t. Your biggest cyber risk might be hiding in the tools you trust every day.
When Your Vendor Becomes the Back Door: What the SolarWinds SEC Case Means for You
The case is gone, but the warning isn’t. Your biggest cyber risk might be hiding in the tools you trust every day.
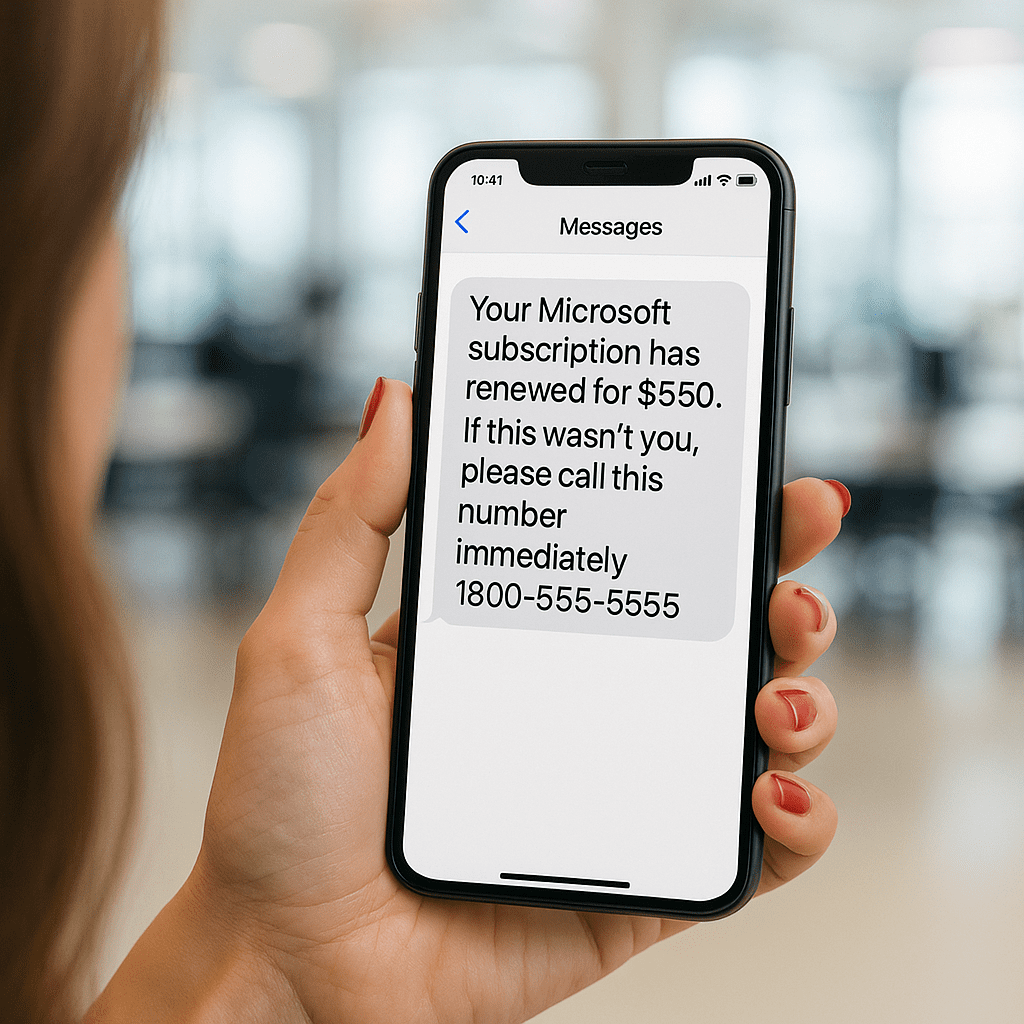
The Anatomy of a TOAD Attack
TOAD attacks look harmless until a “quick phone call” turns into a full-blown breach. Here’s how to keep your business safe.
From the Louvre to Your Inbox: The Art of the Digital Heist
It took seven minutes to rob the Louvre. Here’s what every business can learn from the world’s most famous modern heist.