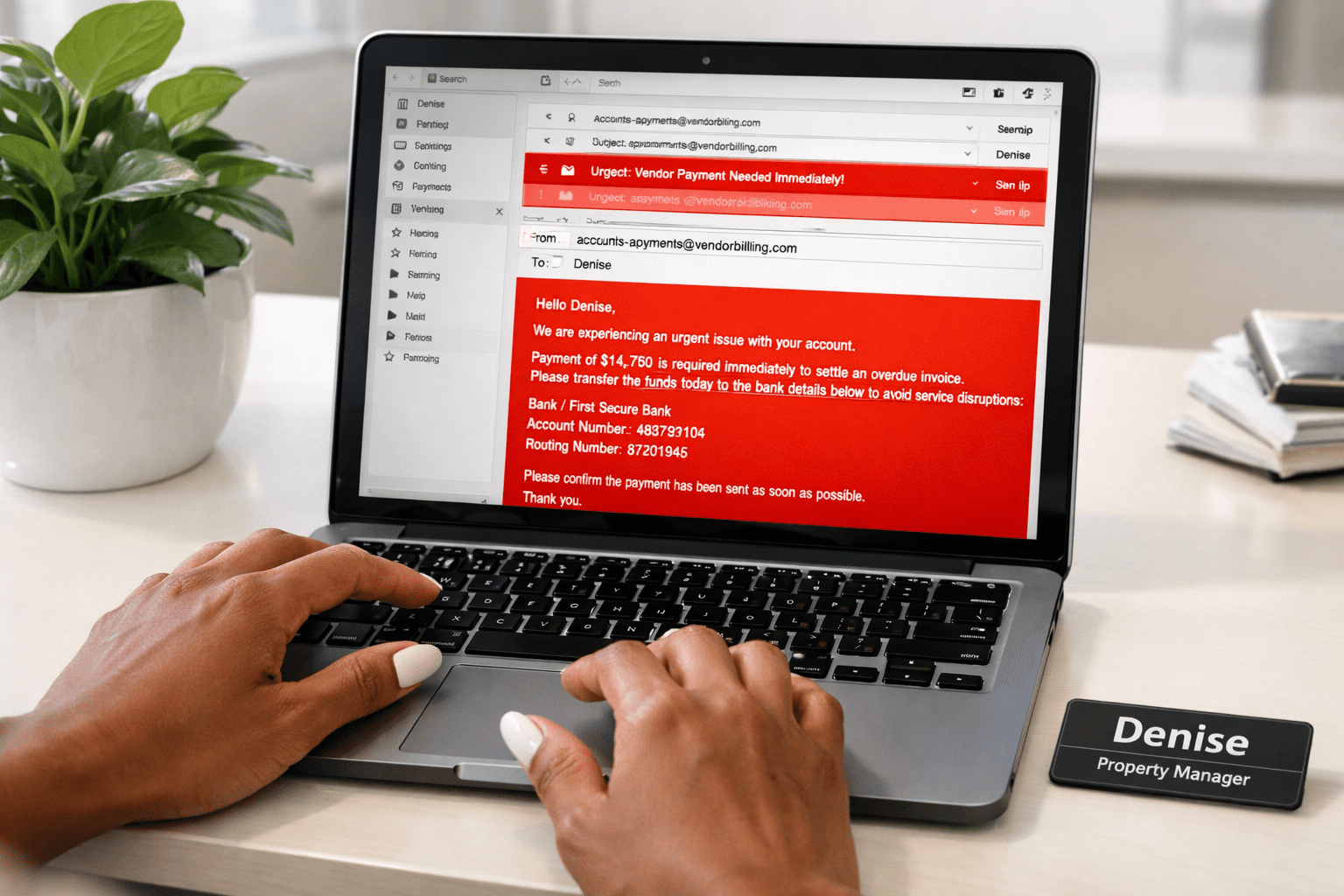
An email comes in. It looks totally normal. It’s from the same vendor you’ve worked with for years. Nothing about it feels out of the ordinary so the invoice attached doesn’t raise any eyebrows.
Nothing feels off, so your employee processes it as usual. Until a few days later when they (and you) realize it wasn’t real.
This kind of thing is happening much more often than most teams realize. Especially in manufactured housing where so much of the day-to-day runs through email.
For a tool that’s integral to the foundation of so many manufactured housing businesses, it begs the question: Why doesn’t anyone take a closer look at it? Why do we always just assume it’ll always work the way it’s supposed to?
There’s actually more that’s happening behind the scenes than most businesses realize, and those configurations quietly determine whether your email is actually protected.
In this blog, we’re going to break down what DMARC, SPF, and DKIM actually do, why they matter more than most people think, and how those small gaps can turn into real problems down the line.
Why Manufactured Housing is Especially Vulnerable
As a manufactured housing operator, you likely rely very heavily on communication. Not just internally, but across a lot of siloed but constantly moving parts. The flow of information going back and forth never ends, and the majority of that runs through email.
Think about it: invoices slated for approval, the payments that are being sent tomorrow, vendors trying to coordinate work, leasing teams following up with last week’s prospects, corporate’s never-ending updates across multiple locations…
Just because email is fast, convenient, and built into the IT framework of your business doesn’t mean that every email is real. Your system can’t automatically verify what’s real and what’s not. That part of the equation is nuanced.
And if you’re managing multiple communities, that complexity just increases. Not everything is centralized, so it can be hard to monitor every nook and cranny, every dark corner. If something looks legit, it usually gets treated that way.
That’s exactly what makes email such an easy entry point. The system isn’t always set up to catch when something isn’t right.
But not to worry, we’re going to take you through the exact things you need to know to make your email system work smarter. Goodbye, shady emails and important messages that never reach the recipient.
What are DMARC, SPF, and DKIM?
Think of these as the three musketeers that sit behind your email system. They decide what gets trusted and what doesn’t. Even though you don’t see them when you send or receive a message, they’re always there, working behind the scenes every time an email hits your inbox.
SPF (not sunscreen) is the starting point. It tells receiving servers which systems are allowed to send an email on behalf of your domain. If something outside that list tries to mimic you, it should raise a bright red flag.
DKIM adds yet another layer. It attaches a digital signature to your emails so the receiving server can verify that the message hasn’t been altered on its route to the intended inbox. It’s a way of confirming that what was sent is precisely what was received.
DMARC is the one that holds the band together. It tells inboxes what to do when something doesn’t pass all the checks. Do we allow it? Do we quarantine it? Or should we reject it entirely?
DMARC matters so much more than people realize, and we’ll bet this is the first time you’re reading about it. Without a clear DMARC policy, even messages that don’t pass the check can still get through. While the checks technically happen, it doesn’t matter because nothing is enforced.
If any of these isn’t configured correctly, everything will still look like it’s working, but there will be a significant gap in how your domain is actually protected.
What Happens When Email Isn’t Set Up Right?
Before we get into how to check whether your email is configured correctly, we need to point out some warning signs that it isn’t.
When these pieces aren’t aligned, the impact doesn’t show up in a way that’s easy to trace back to email. That’s what makes this so important. If you can’t diagnose the issue, the disease spreads. Things still move, messages get sent, and conversations still happen, but there’s less control over what’s being trusted.
For example, an email can be sent to a renter or prospect that looks exactly like it came from your company, even if it didn’t. Or a vendor request can feel so routine that no one on your team stops to question it.
At the same time, perfectly legitimate (and oftentimes important) emails can land in spam without anyone realizing why a response never came.
Over time, this creates real consequences. Think about all of the important decisions that are made over email every day, and if those decisions are based on information that wasn’t verified, communication starts to break down. Big opportunities can be missed, or money can move in the wrong direction.
What makes this even worse is that it rarely points back to that single moment a perfectly valid email ended up in spam. It just kind of feels like things are slipping through the cracks and no one understands why.
The hardest part of this is that there’s usually no clear sign that anything is wrong. Without a dashboard your IT team can check, an alert that your domain is being spoofed, anything to ring the bells, everything just continues as usual.
The assumption is always that email is fine.
Red Flags to Look Out For
When you don’t have visibility into any of this, how would you know for sure that something is wrong?
Valid. But it’s important to understand that this isn’t a surface thing, and without the right tools, you have to diagnose it yourself. Luckily, there are some telltale signs that your email is sick.
Here are some things to look out for:
- Emails going unanswered even when you know they were sent.
- Vendors or partners saying that they never received something (like payment, for example).
- Very interested prospects ghosting you mid-conversation with no clear reason.
- Important messages landing in spam when you know they aren’t or shouldn’t be mistaken as spam.
- Having to double-check whether an email or request is legitimate (you really should be doing this anyway).
- Payment instructions that look and feel slightly off, even if they look right.
- No clear visibility into who can send email on your behalf (meaning using your domain, not your personal email address directly).
- Not knowing who gets sent to spam, who goes to your inbox, who is blocked, who gets quarantined. This is your DMARC policy and you should know it. Yes, you do actually have one.
What to Do About It
Once you start noticing these patterns, the next steps are actually really simple. Now you have to get acquainted with what’s actually happening behind the scenes.
That usually starts with a very simple 5-step checklist:
- Review your DMARC policy and make sure it’s set to enforce (never “none”).
- Confirm which systems are authorized to send emails on your behalf.
- Make sure DKIM is properly set up and aligned. Are your emails digitally signed and verified so inboxes know they’re really from you and haven’t been changed?
- Check where your emails are actually landing by sending some test emails. Are they reaching their intended recipients, or going straight to spam?
- Look for any signs of spoofing and unauthorized sending. Is anyone outside your company sending emails that appear to come from your domain without permission?
Once these pieces are in place, you have visibility, control, and a setup that’s actually protecting your business.
If this all sounds way too complicated, or you have too much on your plate right now, don’t worry. Keep reading.
We Make it Easy
If you’ve never heard of DMARC, SPF, and DKIM, this can all feel really overwhelming. Especially when it comes to how to fix the issues. Now that you have a reason to think about it, it can feel like you need to fix it right now but don’t know where to start.
This is where we come in. We work with manufactured housing operators to review what’s already in place, identify where the gaps are, and tighten things up so you’re not relying on guesses and whims. This includes making sure your domain is authenticated correctly, your policies are enforced, and you have visibility into what’s happening behind the scenes.
We simplify it so that something you rely on every day isn’t exposing you to risk.
If you’re going to be at MHI, we’re running complimentary email security checks at Booth 637. If everything looks perfect, you get to walk away with a completely free Dell backpack. If things are lacking or not looking great, we work with you to help you fix it.
Schedule your on-site 1:1 meeting with us here.
If you’re missing MHI this year but still want to know what’s happening behind the scenes, contact us, and we’ll run through it together (don’t worry, it’s free).
Get clarity before your business is at risk.