When software can be built in days instead of months, the entire development process changes.
AI-assisted tools have made it possible for founders, small teams, and product leaders to spin up working apps faster than ever. Ideas that used to sit in planning documents can now become functioning tools almost overnight.
That speed is powerful.
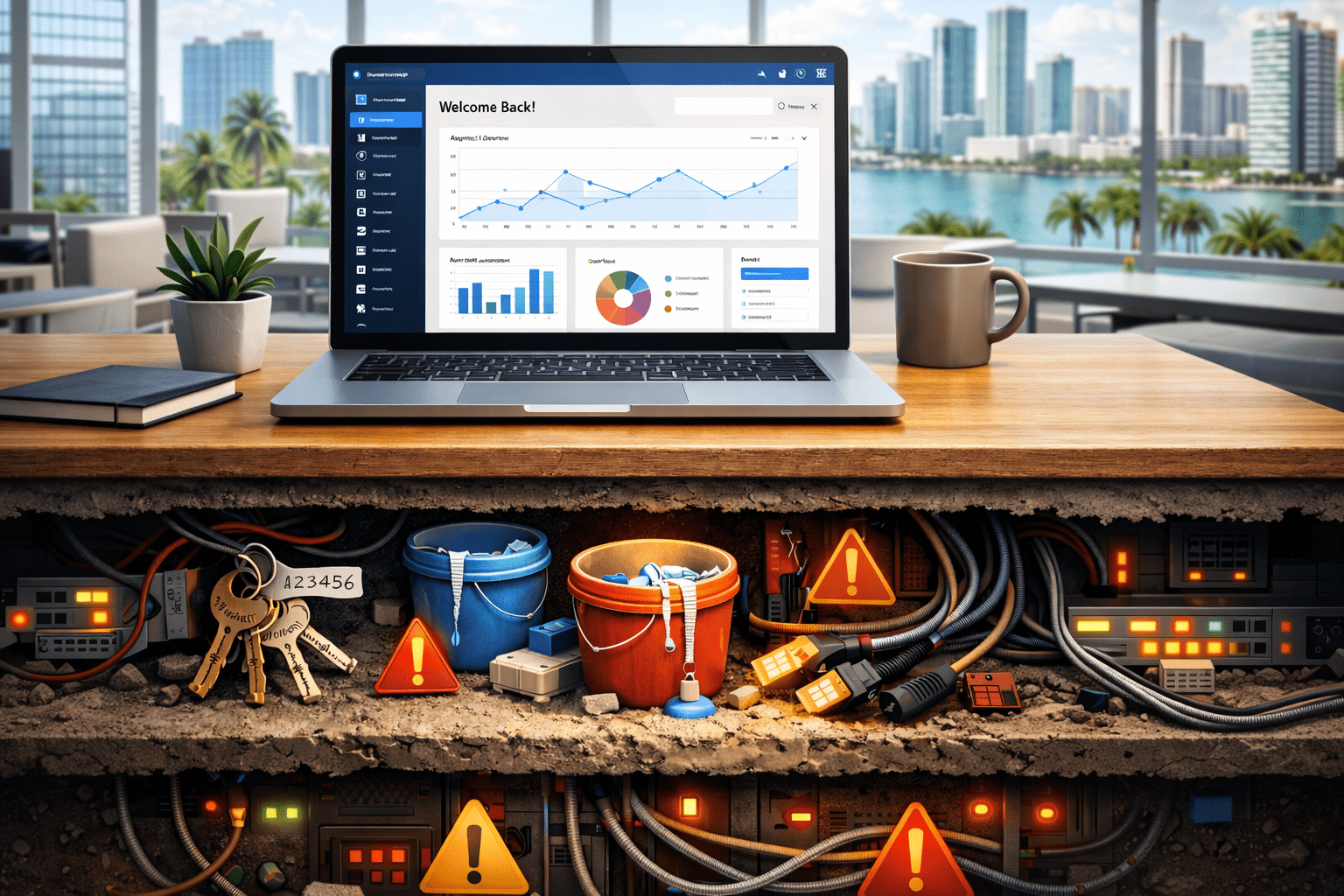
But it also shifts where mistakes tend to happen.
In traditional development cycles, security conversations usually happen during architecture planning. With vibe coding, those guardrails don’t always exist. Code is generated quickly, features come together fast, and infrastructure decisions are usually made later.
That’s where exposure can start to creep in.
Last week, we talked about how vibe coding can move an idea to working software quickly and what it takes to move those apps into a production-ready environment. This week, we’re digging into the part that often gets overlooked: the security risks that build up inside vibe-coded apps and how to spot them before they turn into real problems.
What is Vibe Coding?
Vibe coding is the fast, AI-assisted way many teams are building software today.
Instead of starting with long technical specs and traditional development cycles, builders can describe what they want using prompts in tools like Lovable, Cursor, Claude Code, or Codex to generate working code almost instantly.
Features come together quickly, iterations happen faster, and prototypes can turn into usable applications in a fraction of the time.
That speed is part of what makes vibe coding so powerful and, quite frankly, enticing.
But it also changes how development happens. When the focus is on getting something working quickly, the surrounding pieces like security controls, permissions, infrastructure boundaries, and access policies don’t always get the same level of attention during the early stages.
The code might run perfectly, and the demo might look great. But the environment around that code can still carry hidden risks.
That’s why understanding the security side of vibe-coded apps matters just as much as understanding how they’re built.
When Secrets End Up in Places They Shouldn’t
One of the most common security issues in vibe-coded apps has nothing to do with complicated vulnerabilities. It usually starts with something much simpler: secrets living where they shouldn’t.
When you’re moving quickly, it’s easy to drop an API key into a config file just to get something working. Maybe a token gets added to the frontend during testing. Maybe credentials live in a repository longer than they should. At the time, it’s just temporary. The goal is to get the feature working, not to design a perfect security model.
The problem is that those shortcuts tend to stick around.
Once an app starts evolving, the codebase grows, new features get layered in, and the original “temporary” decisions unintentionally become permanent parts of the system. Credentials remain in places where they’re visible, services are accessible with keys that were never rotated, and logs might even capture sensitive tokens without anyone noticing.
None of this usually causes an immediate failure. The app keeps running, the product keeps improving, and the team keeps moving forward.
But exposed secrets create risk, even if it isn’t a problem right away. If an API key or service credential is discovered, it can give someone access to systems that were never meant to be public in the first place.
This is one of the first things we look for when reviewing vibe-built apps. Most of the time, it’s not a massive problem to fix. It just requires moving secrets into proper environment management, tightening access, and making sure credentials live where they belong.
Fast development is great, but secrets management still needs to be intentional.
Permissions Are Broader Than They Should Be
Another issue that shows up in vibe-coded apps is access control that’s a little too generous.
When you’re building quickly, the priority is usually getting features to work. A database connection gets opened up so the app can read and write data, for example. A service account gets broad permissions so it can interact with multiple systems without errors. Everything functions the way it’s supposed to, and the app moves forward fast, just as the team intended.
The trouble here is that those permissions rarely get revisited.
Instead of narrowing access once the feature works, the original settings often stay in place. A role that was meant to be temporary keeps its high privileges, a database policy allows broader access than the product actually needs, and services trust each other more than they should.
This doesn’t always cause obvious problems right away. In many cases, actually, the app continues to run exactly as expected. Which just adds to this risk.
Broad permissions increase the blast radius if something goes wrong. For example, if a token is exposed or an account is compromised, overly permissive access can allow someone to reach far more of the system than intended.
The goal here isn’t to make development harder, it’s to make sure every service, user, and component only has access to the data it truly needs.
That principle (least privilege) is one of the easiest ways to reduce risk in a vibe-coded app once it starts moving toward production.
Storage Gets Left More Open Than Intended
Another place where risk builds up is storage.
Most modern apps rely on some form of file storage. Users upload images, documents, or other assets, and the application stores them somewhere in the cloud so they can be retrieved later.
When you’re building quickly, the easiest way to get that feature working is to configure storage so the application can read and write freely.
At first, that flexibility makes development easier. Files upload successfully, the interface works the way it should, and the product team can move on to the next feature. But those early configurations, more often than not, remain unchanged once the app moves forward.
Storage that was meant to be temporary ends up publicly accessible longer than expected, access rules stay broader than necessary, and upload paths aren’t always restricted to the users who created the files in the first place.
Nothing looks wrong on the surface; the app continues to function normally.
The problem is that cloud storage is one of the easiest things for attackers to scan.
Automated tools constantly look for exposed buckets and publicly accessible file systems. If storage isn’t properly restricted, sensitive data or user uploads can become visible to anyone who knows where to look.
This doesn’t mean file storage isn’t safe; it just means the access rules around it need to be intentional.
When storage permissions are configured correctly, the application can still function exactly the same way for users, but the underlying data stays protected.
Development and Production Start Blending Together
Another issue we see in vibe-coded apps is that the lines between environments start to blur.
When you’re building quickly, it’s common to run everything in one place. The same database might support testing and real usage. Development services might live in the same environment as production systems. Features get added, adjustments get made, and everything continues to function well enough to keep moving forward.
At first, it seems efficient.
As the app grows, that shared environment starts to pose risks. Changes made during development can accidentally affect live users, debug configurations remain accessible longer than they should, test data and production data begin to overlap in ways that were never part of the original plan.
This isn’t unusual. It’s a natural side effect of building something quickly and evolving it over time.
The challenge is that once an application begins handling real users and real data, those boundaries matter much more.
- Development environments should be isolated.
- Production systems should be protected from experimental changes.
- Access between services should be intentional rather than convenient.
Clear separation between environments is one of the things that turns a fast prototype into a stable system.
Without that separation, small changes can have much larger consequences than anyone expected.
AI Development Moves Fast. Security Debt Moves With It.
None of these issues exist because vibe coding is inherently unsafe.
They show up because speed changes how software gets built.
When development cycles compress from months into days, the focus naturally shifts toward getting something functional as quickly as possible and security controls get added along the way instead of being designed into the system from the beginning.
That’s where security debt starts to build.
During fast dev cycles, small security decisions often get postponed. Credentials may end up stored in places they were never meant to live, access permissions remain broader than necessary so features keep working smoothly, and storage configurations stay more open than they should while the product continues to evolve.
Each of these decisions feels small in the moment. The app works, users can interact with it, and progress continues. What’s wrong there?
The problem is that over time those shortcuts accumulate.
As the application grows, everything around it gets more complex. More services get added, more people start relying on it, and the amount of data moving through the system increases. At this point, the small security decisions made early on can start to carry much bigger consequences.
This is why security reviews become so important once a vibe-coded app begins moving toward production. Fast builds are exciting, but making sure those builds remain safe as they grow is what keeps the product sustainable.
A Security Review for Vibe Coded Apps
None of this means vibe coding is a bad way to build software. In fact, it’s one of the most exciting shifts happening in development right now. Teams can move faster and turn ideas into real products without waiting on long development cycles.
It’s just really important to remember that speed doesn’t remove the need for good architecture and security. Those conversations need to happen sooner, once the product starts taking shape.
That’s where Network Thinking Solutions comes in.
We work with teams who have built something promising. The app works, the product is gaining traction, and the next step is making sure the environment around it is secure, stable, and ready for real growth.
Our team reviews the infrastructure behind the application and looks for the kinds of issues that tend to show up in fast-built projects. That includes exposed secrets, overly broad permissions, storage access, environment separation, and the overall architecture supporting the app.
In many cases, the fixes aren’t massive rebuilds. They’re adjustments that bring the environment back into alignment with how the product is meant to operate.
Vibe coding gets you moving quickly. Network Thinking Solutions helps make sure what you’ve built can run safely once real users, real data, and real traffic enter the picture.
Built an app with AI tools? Let’s make sure it’s secure and ready for production. Get in touch today!