When most people think about cyberattacks, they picture a suspicious email or a weird link, maybe a badly worded message that someone “should’ve known better” than to click.
And yes, email is a problem, but it’s not the whole problem.
Focusing only on phishing is like locking your front door and assuming the rest of the building will take care of itself. It creates a false sense of security, and one that attackers are happy to take advantage of.
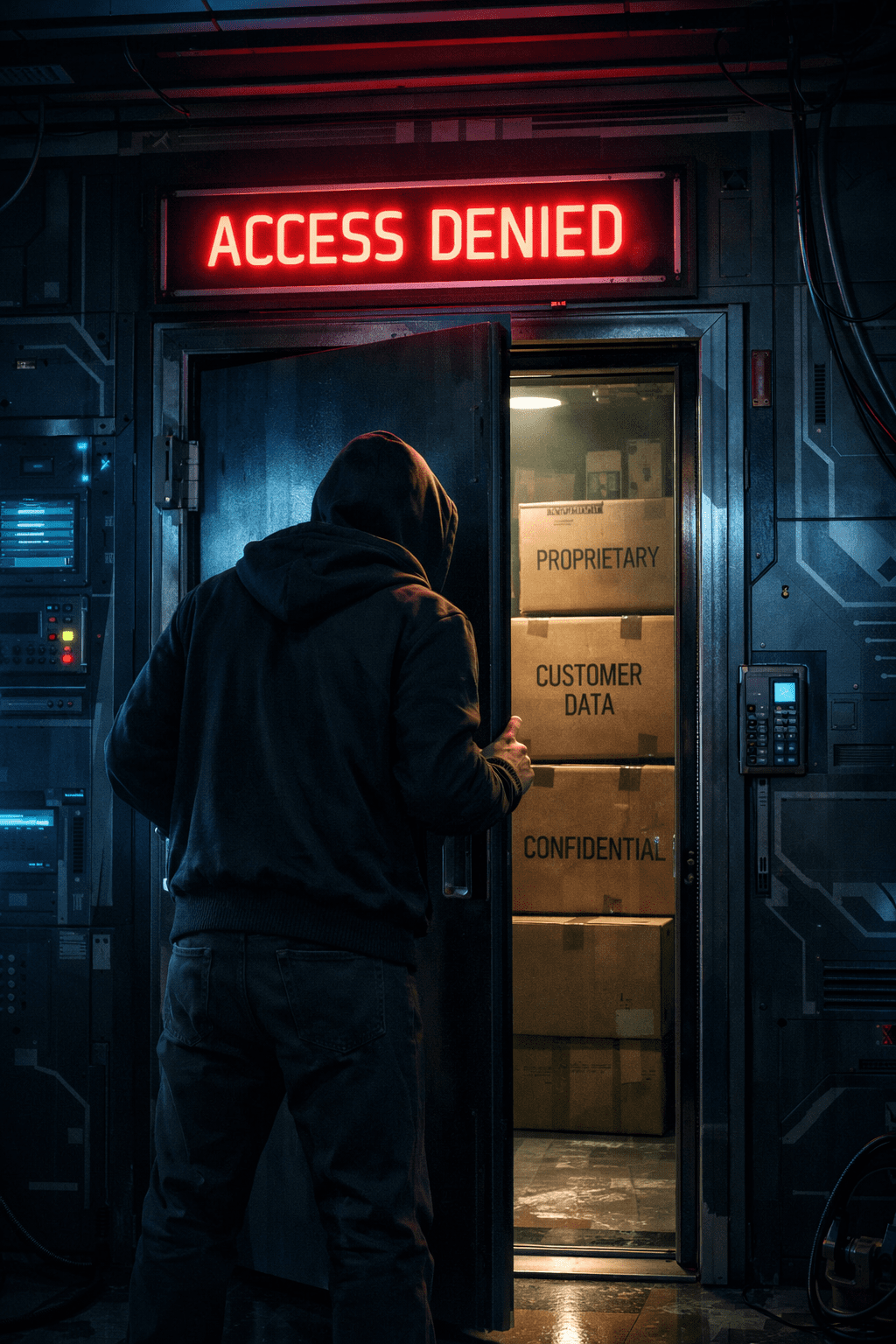
Most successful cyberattacks don’t start with something dramatic. They start quietly, through doors most businesses don’t realize they’ve left open.
To protect your business, you need to understand exactly where threats actually live. Not just the obvious places, but the overlooked ones. Think of them as the side doors, the back entrances, the windows no one thinks to check.
In this blog, we’re going to dive into the most common entry points hackers are using right now. We’ll help you understand where cyber threats start and how to stop them.
What is an entry point?
In cybersecurity, we use the term “attack vector”. It sounds technical and complicated, which is usually where non-IT folks check out.
So, let’s simplify it.
An attack vector is an entry point, and an entry point is just any way into your business systems.
Think of it as any place someone could get access, intentionally or not. Some of those doors are obvious. Others exist because of convenience, oversight, or the assumption that “this probably isn’t a big deal.”
Less hacker smashing a window, and more someone finding a side door that was never locked in the first place.
Entry points can be digital doors (like logins and remote access), borrowed keys (vendors and third-party tools), or forgotten windows (old systems and misconfigurations). Most of them aren’t malicious on their own.
The problem with them is that attackers don’t need new ways in. They look for the paths that already exist and wait for the moment when no one’s paying attention.
Understanding entry points is about awareness. Once you know where those doors are, you can decide which ones need better locks, which ones need monitoring, and which ones don’t need to be open at all.
Entry Point #1: Credentials (Stolen or Reused)
If there’s one entry point that shows up again and again, it’s this one. Passwords are easy to underestimate, and most people don’t change them often enough or, worse yet, keep their default password if they aren’t forced to change it.
A lot of attacks don’t start with someone “hacking” their way in; they start with a login that already works. It could be a reused password from another breach, credentials stolen through phishing, or an old account that just never got turned off.
Once attackers have those credentials, they don’t need to break anything to get in. They just sign in and blend in. From the system’s point of view, nothing looks suspicious because it’s a real user, using a real login, doing things they technically have permission to do.
That’s why stolen credentials are so effective and so hard to spot.
This is also where simple changes make a huge difference. Use unique passwords, get a secure password manager, and use multi-factor authentication even if it adds an extra step. None of these are flashy, but together they turn a single stolen password into a dead end instead of an open door.
If attackers can’t log in, they have to work harder, which they don’t want to do.
Entry Point #2: Vendors and Third-Party Software
Most businesses think about security in terms of what they control, but a huge amount of access lives outside those walls.
Every vendor you use becomes a potential entry point (scary, we know). Your accounting software, the CRMs you use on a daily basis, property management platforms, remote support tools… Anything that integrates with your systems or holds your data carries its own risk.
The tricky part is that this access is usually intentional. Vendors need permissions to do their job. Think of your tech stack and all of the tools that get automatic updates, the integrations that run quietly in the background. You probably don’t think much about it until something stops working.
This is exactly why vendor-based attacks are so effective. They look like normal business activity coming from a trusted source. When a vendor gets breached, attackers don’t just steal data and leave; they look for what that vendor can reach next.
If attackers gain:
- vendor login credentials
- access to their update systems
- control over their support tools
They inherit the same permissions to your systems that the vendor had. That means attackers don’t have to “hack” you directly, they just stroll in wearing your vendor’s badge.
Most businesses never ask how much access their vendors actually have, what happens if one of them gets compromised, or how quickly they’d even notice. That blind spot is what attackers count on.
Vendor risk doesn’t mean “don’t trust anyone.” It means knowing who has a key, what doors it opens, and whether anyone is paying attention when that key gets used.
Entry Point #3: Remote Access Tools
Remote access tools exist for a good reason. IT support needs them, vendors use them, and internal teams rely on them to work from anywhere. On paper, they’re incredibly helpful, but in practice, they’re also a favorite entry point for attackers.
The problem is what happens when access sticks around longer than it should, gets reused, or isn’t monitored closely. A tool that was set up for a quick fix months ago can quietly become a permanent backdoor into your systems.
Attackers actively look for exposed remote desktop connections, poorly secured VPNs, and support tools protected by weak or shared credentials.
What makes this entry point especially dangerous is how normal it feels. Remote access activity doesn’t raise eyebrows. Someone logging in remotely looks like… well, work. Unless you’re watching behavior in addition to access, it’s easy to miss when that access is being abused.
Don’t throw your remote access tools out the window just yet. Get better guardrails, like limited permissions and strong authentication. Also, look into monitoring that notices when something doesn’t match how your business actually operates.
A door you meant to open briefly shouldn’t stay open forever.
Entry Point #4: Unpatched or Forgotten Systems
Some of the easiest doors into a business aren’t hidden at all. They’re just old.
Remember, every system has vulnerabilities. That’s normal. The risk shows up when those vulnerabilities are publicly known and never fixed. Some examples of these would be an outdated server, a piece of software no one wants to touch because “it still works,” a machine that got left behind during an upgrade and quietly kept running.
Attackers love these systems because they don’t require much brain power. If a vulnerability has been around long enough, someone has already written a playbook for exploiting it.
The dangerous part is that unpatched systems rarely cause immediate problems because everything appears fine until one day, it isn’t. And by then, the system that was ignored becomes the easiest way in.
This is why, when you think about patching, it isn’t about perfection. You just need to remove low-effort opportunities. When you stay current, attackers have to work harder, which they really don’t want to do.
Entry Point #5: Misconfigured Cloud Services
Moving to the cloud feels like a security upgrade by default because you are trusting someone else to host and maintain it. Surely that means it’s safer, right?
Not always.
Cloud platforms are powerful, but they’re also flexible, and that flexibility cuts both ways.
The most important thing to remember about moving to the cloud is that cloud providers secure their infrastructure, not your configuration. That’s up to you.
Attackers know this, so they actively scan for exposed cloud resources and misconfigurations because they don’t require breaking in. They’re just there, waiting to be found.
Understanding how your cloud environment is configured helps you ensure that your data is actually secure.
How Visibility and Layered Security Change the Outcome
If attacks are quiet, then blocking a single loud threat isn’t enough.
This is where a lot of security strategies fall apart. They’re built around one idea: stop the bad thing at the perimeter. But modern attacks don’t come from one place, and they don’t rely on one mistake. They move through credentials, vendors, remote access, cloud services, and systems that already belong there.
That’s why visibility matters more than any single tool.
At Network Thinking Solutions, we don’t rely on one product to save the day. We build layered security on purpose, and the overlap is the point.
When one layer misses something, another catches it. And instead of finding out after damage is done, you have eyes on what’s happening as it happens.
You don’t need perfect security. You need awareness and the ability to act before a small issue turns into a major incident.
If you want a clearer picture of where your real entry points are and how exposed your business actually is, get your complimentary cybersecurity assessment today. One hour is worth your peace of mind.