We’re back with Part 3 of our CheckoutChamp saga. This time, pulling back the curtain on how we built real monitoring in a platform that wasn’t designed for it.
In Part 1, we broke down the hidden risks in website funnels and why they’re such an attractive target for attackers. In Part 2, we walked through a real-world case where malicious code kept coming back, not just once, but again and again, showing just how persistent these threats can be when access gaps exist.
But there was still one big piece missing: visibility.
Cleaning code is one thing, but without monitoring in place, there’s no way to know if the same problem shows up tomorrow or next week. That’s exactly the position we found ourselves in with CheckoutChamp.
Our client needed alerts. They needed to know when funnel pages changed, and whether those changes included malicious code.
The catch? CheckoutChamp doesn’t provide an API for funnel scanning. No API means no straightforward way to pull data from thousands of funnel pages, and without that, monitoring at scale is almost impossible.
This was more than just a technical roadblock; it was a business risk. If changes were happening behind the scenes, the client’s customer could lose trust before they even had a chance to react. So we had to find another way.
That’s where Part 3 comes in: how we engineered visibility where none existed.
The original challenge
The problem wasn’t just malicious code slipping into CheckoutChamp funnels. We’d already seen how that played out in Part 2. The bigger challenge was figuring out how to keep eyes on those funnels after cleanup.
Our client needed monitoring. They wanted to know when funnel pages were changed, and whether those edits looked suspicious. The complication? CheckoutChamp is technically their client’s platform, not theirs. That meant we couldn’t simply plug in traditional monitoring tools or rely on built-in reporting because those features don’t exist.
No API. No alerts. No easy way to track changes across thousands of pages. Without visibility, our client would always be reacting after the fact, instead of catching issues as they happened.
So the question became: how do you give a business visibility into something they technically don’t own, using a platform that doesn’t offer the tools you’d expect?
What we did
To bridge the visibility gap, we had to get creative.
With no official API available, we looked under the hood of CheckoutChamp and reverse-engineered parts of its web interface. That let us tap into a front-end API that wasn’t designed for monitoring but gave us just enough access to start pulling data from funnel pages.
From there, we fed page content into Google AI for evaluation. Instead of trying to manually review every single funnel, AI helped shrink the scope by flagging questionable pages. Those results were pushed into a dedicated Slack channel, where the client’s client could see updates in real time.
It wasn’t the out-of-the-box solution that CheckoutChamp envisioned for its platform, but it gave our client the visibility they needed, without waiting for a feature that didn’t exist.
The technical challenges
Getting monitoring in place wasn’t straightforward. CheckoutChamp doesn’t provide the kind of APIs you’d expect for funnel auditing, and the permissions we had didn’t include things like IP logs or detailed activity history.
In other words: the usual visibility tools weren’t there.
That’s where the workaround came in. By tapping into the platform’s front-end behavior, we were able to surface funnel changes, run them through Google AI for review, and push structured results into Slack.
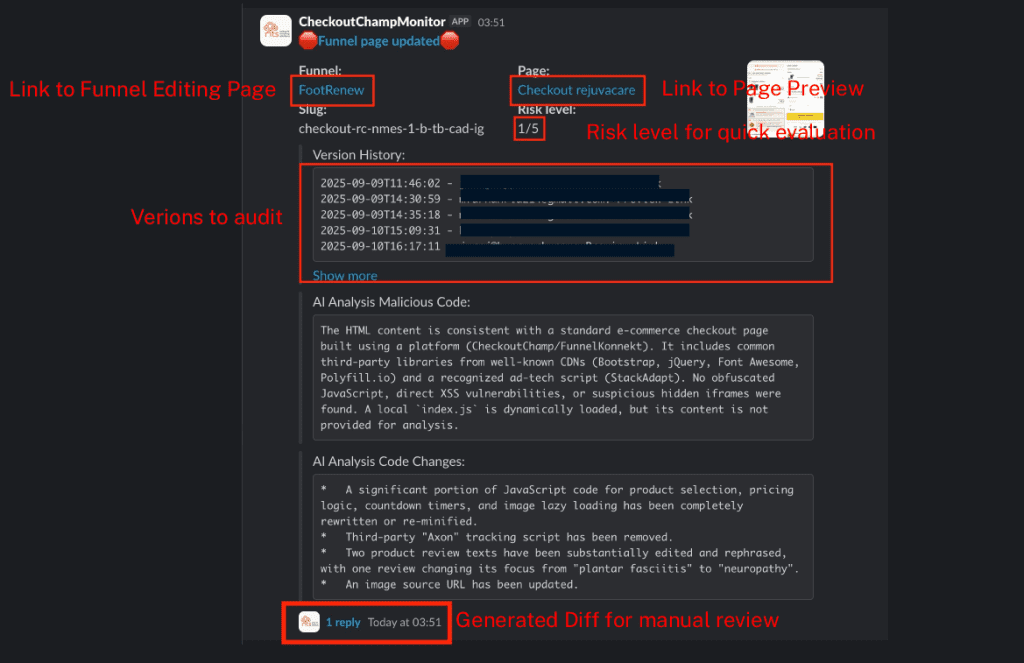
The screenshot above shows what that looked like in practice:
- Links to funnels and page previews made it easy to jump directly into the source if something looked suspicious.
- Version history allowed us to quickly identify what had changed, and when.
- Risk scoring gave a quick, at-a-glance evaluation of whether a change might be malicious.
- AI-generated analysis summarized what the code was doing — from JavaScript edits to suspicious tracking scripts.
- Diff outputs (at the bottom) let us manually review exactly what was added, removed, or rewritten.
It wasn’t the way CheckoutChamp intended their product to be used, but it gave our client’s client what they really needed: continuous monitoring and actionable visibility into funnel changes.
Expanding the method
Once the system was working for CheckoutChamp, it became clear that the same blind spots existed elsewhere. Funnelish, another funnel platform, has the same limitations, such as no real API access, no straightforward way to track edits, and no built-in monitoring.
The process we developed didn’t just solve one problem. It gave us a repeatable way to monitor platforms that weren’t designed with visibility in mind. By reusing the same approach—pulling front-end data, running it through AI, and surfacing the results in Slack— we extended coverage beyond CheckoutChamp.
For our client, this meant more than just patching a single hole. It gave them a framework they could rely on for ongoing monitoring across multiple platforms their clients use, even when those platforms don’t offer the tools you’d normally expect.
Lessons learned
What started as a code cleanup turned into something bigger: a way to monitor platforms that don’t make monitoring easy.
Without official APIs, log access, or MFA, the usual playbook didn’t apply. But by reverse engineering the front-end, layering in AI, and piping results into Slack, we created a workflow that gave real visibility back to the people who needed it.
The takeaway is simple: you can’t always wait for a platform to give you the tools. Sometimes you have to build your own.
At NTS, that’s exactly what we do.
We don’t just secure environments when everything lines up neatly; we find ways to solve the tough problems, the ones that don’t have a built-in answer. Whether it’s CheckoutChamp, Funnelish, or any other SaaS tool your business relies on, we’ll figure out how to give you the visibility and control you need to stay secure.
If you’re tired of reacting after the fact and want to stay ahead of hidden threats, let’s talk.