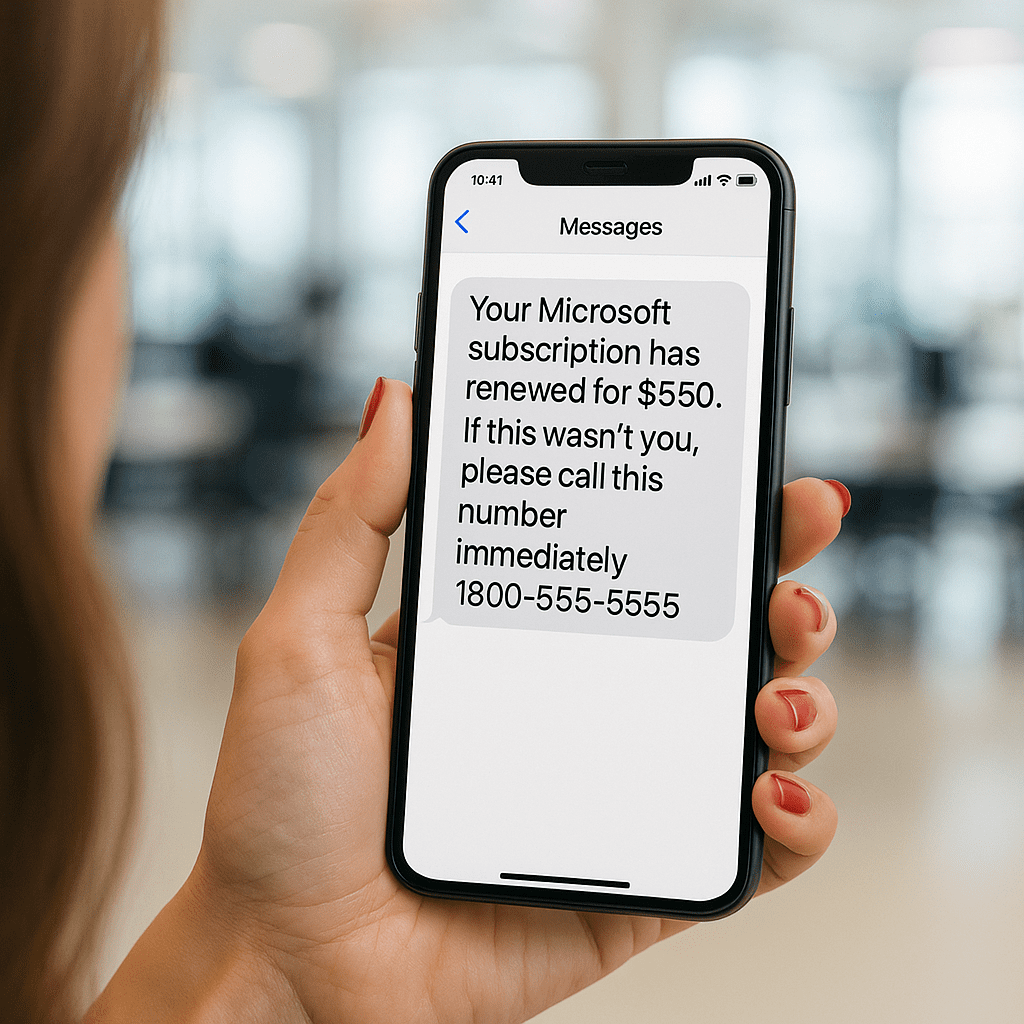
If you’ve ever opened an email that made your heart drop for a second— “Your subscription has renewed for $349.99,” “Unauthorized charge detected,” “Call immediately to avoid account suspension”—congratulations, you’ve brushed up against a TOAD attack
No, this has nothing to do with frogs.
A TOAD attack is one of the sneakiest phishing scams out there because it flips the script.
Instead of tricking you into clicking a bad link, attackers trick you into calling them. When you call, the real scam begins. Credential theft, remote access, “refunds” that drain your bank account, all of it. It’s sneaky, but it’s effective because it gets past all of those meticulously built cybersecurity defenses.
The worst part is, most people fall for it because calling feels safer. It feels human. It feels official.
That’s exactly why TOAD attacks are exploding right now.
In this blog, we’re breaking down how these scams actually work, why they’re so effective, and what it takes to keep your business from getting caught in one.
What is a TOAD attack?
A TOAD attack is basically phishing with better acting. Instead of sending a sketchy link, hackers send a legit-looking email that pushes you to call a phone number. For operators who are constantly juggling a dozen things (community managers, real estate teams, SMB owners, anyone wearing 15 hats at once), this is exactly the kind of message that slips through the cracks.
Picture this:
You run multiple communities, your inbox is a war zone, you’ve got vendor questions, resident issues, invoice approvals, and a dozen small fires nobody warned you about.
Then you see it:
“Your account has been charged $349.99. Call immediately if this wasn’t you.”
If you’re like most busy operators, you don’t have time to dissect it. It’s the end of the year, there’s too much going on, and the $350 you didn’t budget is about to get you in a world of trouble. So what do you do? You call the number in the message.
That’s the trap.
On the other end of the line isn’t Microsoft or Amazon or your billing department. It’s a scam call center trained to sound official, build urgency, and walk you right into giving up access like passwords, banking info, or even remote control of your computer.
For a lot of overwhelmed operators, small teams, businesses without a full IT department, this type of scam hits hard because it preys on speed, stress, and the absolute need to “just fix it quickly.”
TOAD attacks work because they feel safe. They feel like customer service, and they feel like the fastest way to solve a problem.
But they are designed to open the door to a much bigger one. Let’s take a closer look at how, exactly, this plays out.
The Anatomy of a TOAD Attack
TOAD attacks aren’t random. They’re scripted, structured, and designed to get a busy, overwhelmed person to act fast without asking questions. Here’s what it looks like in real life:
1. The Setup: A “Routine” Email Lands in Your Inbox- It looks like a billing notification, renewal receipt, refund alert, or a fraud warning. Nothing wild. Nothing obviously malicious. Just annoying enough that you want it handled now. For operators juggling multiple communities or real estate teams managing dozens of transactions, this is the kind of email you clear before your coffee gets cold.
That’s the whole point.
2. The Hook: The Phone Number- Instead of pushing you to click a link, the email gives you a number to call. Here’s the psychological trick: Calling feels safe, where clicking does not. So most people think they’re playing it safe by dialing. Except the number doesn’t go to Microsoft, Amazon, Norton, or your bank.
It goes straight to a scam call center.
3. The Call: The Social Engineering Starts Fast- This is where the real attack begins. The person on the line sounds polished, calm, warm, and helpful. They validate your concern and create urgency. They speak in “support language” that feels familiar.
And before you know it, they’re guiding you to:
- Log in to an account (so they can steal credentials)
- Install a remote access tool (so they can take control)
- “Verify” payment info (so they can drain funds)
- Process a “refund” that leads to financial loss
Every step feels logical in the moment, helpful even. Especially when you’re already stressed or rushing.
4. The Payload: What They’re Actually After- Once the attacker has a foothold, things can escalate quickly:
- Remote access to your device
- Full entry into the company email
- Movement across your network
- Access to sensitive files, billing systems, or resident data
- Wire fraud and invoice scams
For a small team or a company with limited IT oversight, this can go undetected until the money is already gone.
5. The Exit: They Disappear Before Anyone Notices- The attacker closes the call politely, sometimes even saying, “We’ve resolved the issue for you.” Meanwhile, they’ve installed tools, captured credentials, or set up a way back into your systems. Because the victim called them, there’s less suspicion, which gives them more time to operate in the background.
Why TOAD attacks work so (dang) well
TOAD attacks work because they exploit something every busy person in Q4 knows too well: There’s never enough time in the day. When you’re juggling requests, vendor calls, calendar madness, and the hundred quiet problems no one else sees, you’re not sitting around analyzing every email that hits your inbox; you’re triaging.
You’re moving fast. And attackers know it.
The brilliance of a TOAD attack is that it feels safe. We keep mentioning this, because it’s true. There’s no sketchy link, no malware attachment, nothing your instincts normally flag. It reads like a billing issue, an account alert, or a routine subscription notice. The kind of admin clutter you deal with ten times a week. Also, Calling has always felt safer than clicking.
Once they get you on the phone, the psychology shifts. You’re talking to a real human voice.
They sound professional. They speak in a tone that mimics billing departments and support desks. They act like they’re helping you fix a problem you didn’t ask for but definitely want resolved. When speed matters, most people will take the fastest path to resolution, which is exactly what these attackers are counting on.
It also doesn’t help that traditional security tools don’t catch TOAD attacks.
Combine all of that with small teams, overstretched staff, and the nonstop pace of SMBs…well, you’ve got an attack that can slip right through the cracks without anyone realizing something’s wrong until the damage is already done.
How to Protect Your Business From TOAD Attacks
The good news is that TOAD attacks aren’t unstoppable. They thrive on speed, stress, and confusion, which means the best defense is giving your team simple, repeatable habits that break the attacker’s script.
Protection doesn’t start with expensive tools or complicated workflows; it starts with one core principle:
If an email tells you to call a number, don’t. It really is that simple.
That one habit alone shuts down most TOAD attacks instantly. But there are a few more guardrails that make a big difference for operators and small business teams.
First, create a clear internal rule: If something looks like a billing alert, refund notice, subscription renewal, or fraud warning, verify it through known channels, not the phone number in the email. Go to your dashboard, your vendor portal, your bank’s website. Look for the actual support line on the back of your card. Anywhere that isn’t the number in the message.
Next, make sure MFA is turned on everywhere you can put it. Even if someone accidentally gives up a password, MFA stops attackers from walking right into your accounts. It’s also worth locking down remote access tools. Most TOAD attacks depend on convincing someone to install one of these tools during the call.
And finally, keep a pulse on your environment. The sooner you spot a weird login attempt or an unexpected app installation, the faster you can shut down the attack before it spreads.
These steps aren’t complicated, and that’s the point. The easier you make good security habits, the harder TOAD attacks become.
Security shouldn’t be another fire you have to put out
If all of this feels overwhelming, you’re not alone.
TOAD attacks are sneaky by design, and the people behind them are professionals at catching busy teams off guard. Most of the operators, property managers, and SMB leaders we work with aren’t sitting around analyzing every email. You’re running communities, serving residents, managing staff, and putting out fires. You don’t have time to memorize every new scam that pops up.
And honestly, you shouldn’t have to.
That’s where NTS comes in. Our job is to pay attention to threats like this so you don’t have to. We monitor your environment, lock down the weak spots, and help your team build simple habits that stop these attacks before they turn into real damage.
You handle the business, we handle the “someone just called Amazon but it wasn’t actually Amazon” moments.
If you want a cybersecurity partner who can keep an eye on this stuff, guide your team, and give you the confidence that someone competent is watching the door, let’s talk. We’re here to make security feel manageable.